Administrative access to routers, switches, firewalls, and other network devices represents one of the highest-risk areas in enterprise security. When privileged access is not centrally controlled, organizations face credential exposure, configuration errors, and limited visibility into user activity.
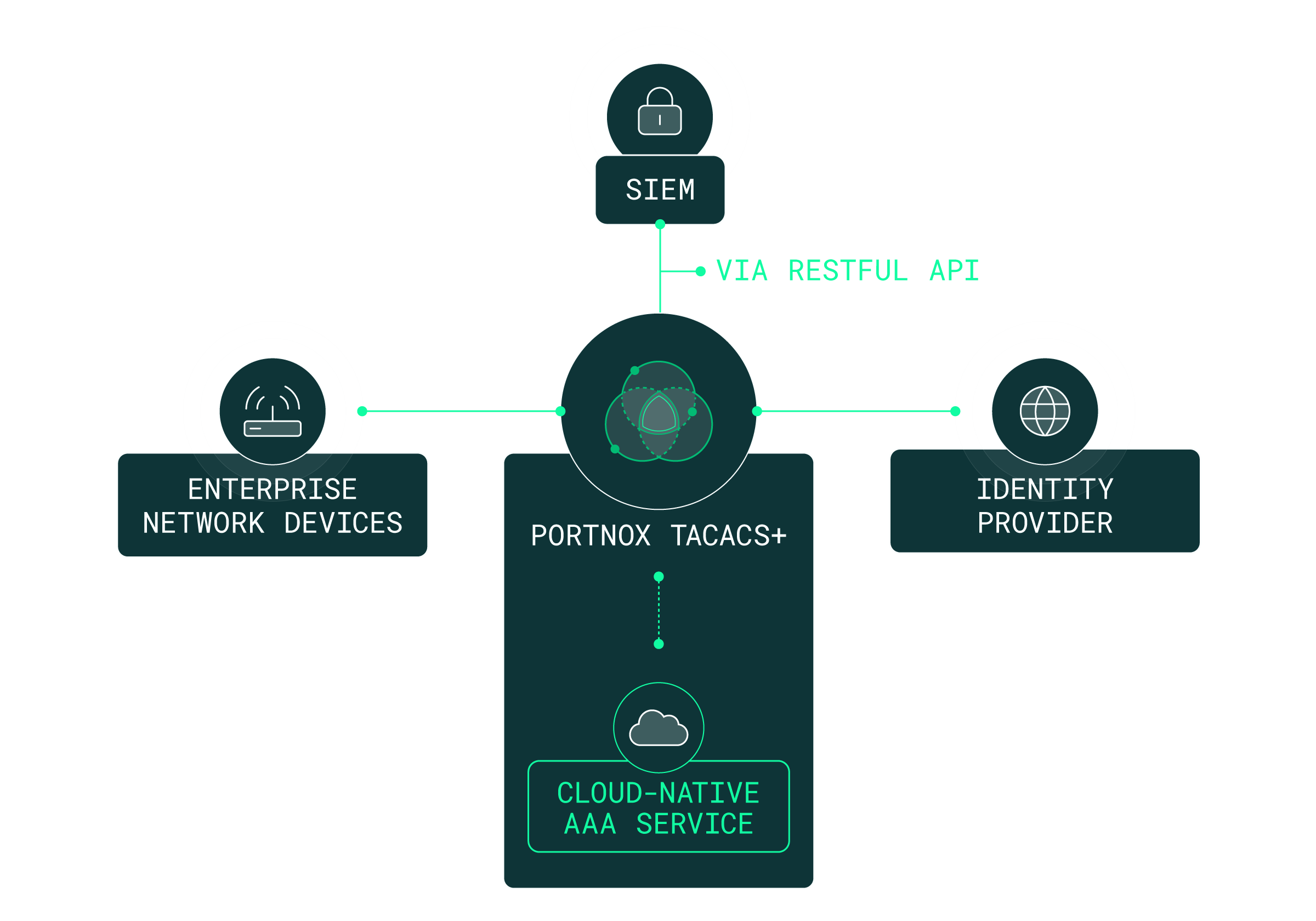
Portnox delivers cloud-native TACACS+ solutions that centralize authentication, authorization, and accounting (AAA), securing device administration without infrastructure complexity.
TACACS+ (Terminal Access Controller Access-Control System Plus) is a centralized AAA protocol used to secure device administration. It verifies user identity, enforces granular command authorization, and records user activity for audit and compliance purposes.
Unlike alternatives that combine authentication and authorization into a single function, TACACS+ separates these processes. This separation enables precise command-level access control, making TACACS+ the preferred approach for securing network administrator access to routers, switches, and firewalls.
For enterprise network security, TACACS+ ensures that privileged access is controlled, enforceable, and fully auditable.
Enterprise networks rely on privileged access to critical infrastructure. However, traditional administrative access models often create security blind spots and operational friction.
Common challenges include:
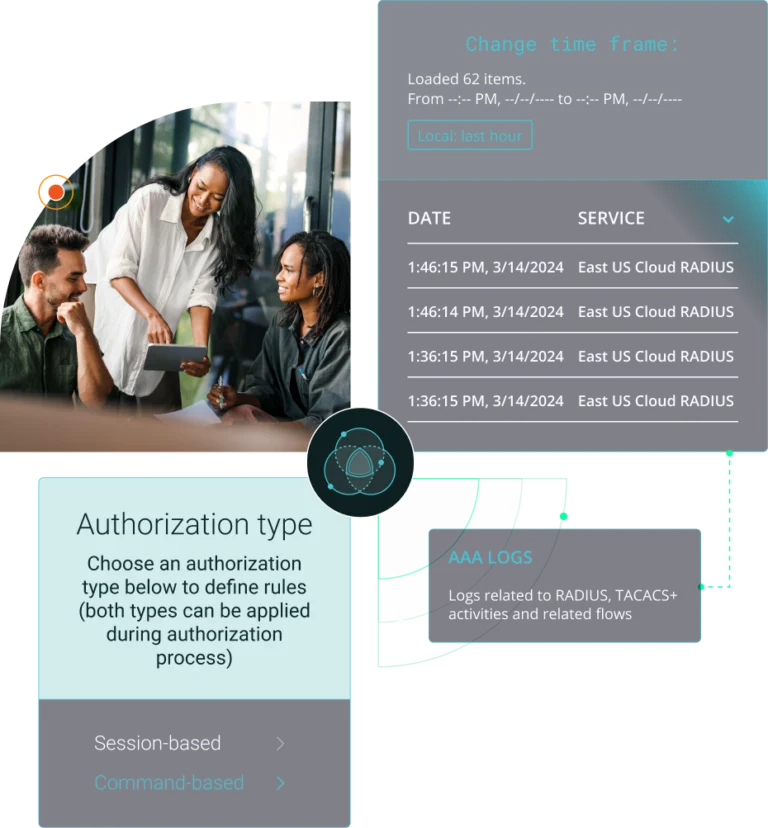
Portnox Cloud delivers TACACS+ as a fully cloud-native service, eliminating on-prem server infrastructure while preserving strong administrative access control. Authentication integrates with Microsoft Entra ID, Okta, and Active Directory across distributed environments.
Portnox enables:
Enterprises choose Portnox because it modernizes TACACS+ delivery without infrastructure complexity. Strong access control should not increase administrative burden — Portnox simplifies onboarding, centralizes policy updates, and integrates seamlessly with existing identity systems.
Key differentiators include:

TACACS+ plays a critical role in compliance and governance initiatives. Enterprises must demonstrate separation of duties, enforce role-based authorization, and maintain proof of who accessed what and when.
Portnox supports compliance through centralized logging, granular authorization policies, and detailed accounting of user activity. This strengthens governance controls while maintaining operational efficiency.
With Portnox’s TACACS+, you can manage your infrastructure whether you have 10 devices or 10,000, while reaping all the benefits of our cloud-native platform. Implement least-privileged access down to the individual commands and get seamless integration with your existing security tools and identity provider. Plus, no more late-night upgrades or patches!

Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.
TACACS is a centralized authentication, authorization, and accounting (AAA) protocol used to control administrative access to network devices. Organizations use TACACS+ to verify user credentials, enforce command-level authorization, and log administrative activity for audit and compliance.
TACACS+ authentication verifies user credentials against a centralized server before granting access to a network device. After authentication, authorization policies define which commands can be executed, and accounting records all administrative actions.
RADIUS is typically used for user network access authentication, while TACACS+ is designed for administrative control of network devices. TACACS+ separates authentication and authorization functions and provides granular command-level access control for network administrators.
TACACS+ encrypts the entire packet body during communication between a network device and the TACACS+ server. This protects authentication credentials and authorization data from interception during transmission, strengthening secure administrative access.
TACACS+ uses TCP port 49 for communication between network devices and the TACACS+ server. Organizations configure firewalls to allow secure administrative authentication and authorization traffic over this port.
TACACS+ is well-suited for enterprise environments because it centralizes authentication, enforces granular command authorization, and provides detailed accounting of administrative activity. Cloud-native TACACS+ solutions improve scalability, audit readiness, and operational efficiency across distributed infrastructures.
Yes. Modern TACACS+ solutions integrate with identity providers and IAM systems such as Microsoft Entra ID and Okta. This allows organizations to centralize user identities and enforce consistent administrative access policies across network devices.
After completing the form, an email will be sent to you with the report download link.